While conventional penetration testing remains constrained by manual effort, scheduling limitations, and point-in-time assessment scope, this managed service transforms security validation into a continuous, automated function. Central European engineers design, execute, and optimize testing campaigns that operate across the full spectrum of offensive security techniques: automated vulnerability discovery and risk scoring, controlled exploitation validation, comprehensive network mapping and segmentation analysis, protocol and application fuzzing, credential security testing, and configuration weakness identification.
"Organizations require security testing that matches adversary sophistication without demanding internal offensive security teams," stated Frederick Roth, Chief Information Security Officer at CypSec. "Our managed service delivers exactly that: continuous, expert-engineered penetration testing that identifies exploitable pathways before adversaries do. Customers define testing scope and risk tolerance; we handle technical execution, result validation, and remediation guidance."
The service architecture leverages CypSec’s engineering heritage in vulnerability research, exploit development, and adversary simulation. Testing methodologies incorporate current threat intelligence regarding active exploitation techniques, ensuring validation scenarios reflect real-world adversary capabilities rather than theoretical vulnerabilities. Automated engines execute systematic reconnaissance and testing procedures, while specialists validate findings, eliminate false positives, and contextualize results within customer operational environments.
Managed service delivery encompasses complete lifecycle support. Initial engagement involves collaborative scope definition, such as identifying critical assets and testing boundaries, operational constraints, and compliance requirements. Senior engineers then configure testing infrastructure, establish safe execution parameters, and initiate automated campaigns. Continuous monitoring ensures testing effectiveness while preventing operational disruption. Findings are validated, prioritized by exploitability and business impact, and delivered through actionable reports with clear remediation guidance.
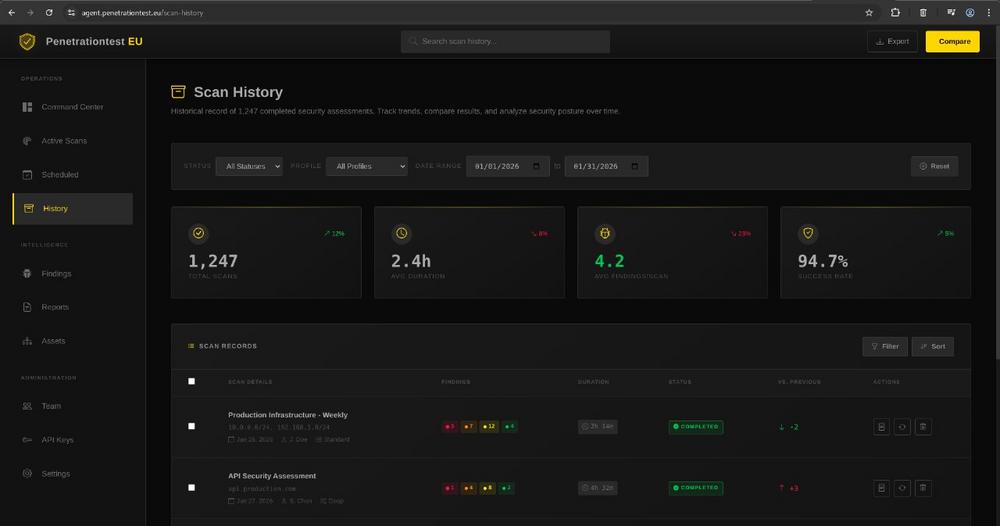
The technical platform integrates multiple specialized engines working in coordinated orchestration. Vulnerability scanners map attack surfaces and identify known weaknesses. Exploitation frameworks validate vulnerability exploitability under controlled conditions. Network mappers visualize infrastructure topology and identify segmentation weaknesses. Fuzzing engines probe application and protocol implementations for unknown vulnerabilities. Credential testers evaluate authentication security. Configuration analyzers identify security control weaknesses. Results correlate across engines, eliminating redundant findings while surfacing complex multi-step attack pathways that isolated testing would miss.
Continuous testing schedules adapt to customer operational requirements, ranging from continuous low-intensity monitoring to intensive pre-release validation windows. Testing intensity modulates based on environmental sensitivity, with safe execution parameters ensuring business continuity. Seciroty specialists review all findings before delivery, validating technical accuracy and operational relevance.
Comprehensive reporting provides multiple stakeholder perspectives: technical teams receive detailed vulnerability information with exploitation evidence and remediation procedures; security leadership receives risk-prioritized summaries with trend analysis and strategic recommendations; executive stakeholders receive business-impact-focused assessments linking security findings to operational risk and compliance posture.
The service includes full engineering support throughout the engagement. Technical consultations clarify findings and remediation approaches. Emergency response capabilities address critical vulnerability discoveries requiring immediate attention. Quarterly business reviews assess testing effectiveness, adjust scope based on environmental changes, and identify emerging testing requirements.
Availability begins on March 15, with enterprise and government customer onboarding typically completing within two weeks of engagement initiation. Organizations interested in evaluating capabilities may request demonstration testing against representative environments to validate technical effectiveness and operational fit.
A webinar session providing detailed technical overview and operational demonstration is scheduled for calendar week 14, 2026 (March 30 – April 3).
CypSec is an international cybersecurity company providing integrated security ecosystem solutions and managed services for government, defense, critical infrastructure, and enterprise clients. The company combines proprietary software platforms with senior practitioner expertise to deliver comprehensive protection without surrendering client operational autonomy.
CypSec Group
Suite 801, 5500 North Service Road
CDNL7L 6W6 Burlington, Ontario
Telefon: +31653169442
https://cypsec.de/
Chief Executive Officer
Telefon: +31653169442
E-Mail: daria.fediay@cypsec.de
![]()